Third party and cloud: Regulatory challenges
Companies are forming more frequent and complex relationships with third parties, introducing new or elevated risks.

Driven to enhance competitiveness, expand operations, and accommodate customer needs, financial services companies are forming more numerous and complex relationships with third-party companies at significant speed and scale, including financial technology-focused entities such as cloud service providers. These relationships offer advantages but can also reduce management’s direct control of activities, which may introduce new risks or elevate existing risks for companies and their customers.
Explore here insights from the KPMG report Ten key regulatory challenges of 2022.
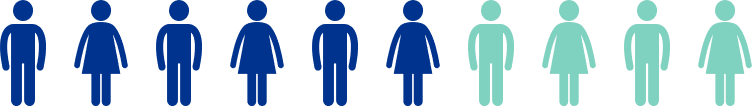
Six in 10 respondents (59%) warn that their technology still does not give them "anywhere near the visibility they need" to manage third-party risk across the supply chain.
Source: KPMG TPRM Survey Outlook 2022 (early 2022 release)
Mitigating risk: Third party and cloud
Centralize and automate third party risk management (TPRM) processes while executing a resilient vendor strategy.
Centralizing and automating TPRM processes can serve to:
- Allow for a standardized, repeatable, and scalable process that can increase efficiency and reduce costs
- Improve consistency in risk identification, risk prioritization, and communication
- Inventory and group vendors and technology providers by risk category, highlighting overlaps/strategic duplications
- Prompt vendor reviews and risk assessments based on “triggers”
- Formalize roles and responsibilities, including decision-making.
The federal banking agencies (FRB, OCC, FDIC) have proposed joint TPRM guidance to promote a consistent supervisory approach and “clearly articulate risk-based principles on third-party risk management.” Additional regulatory releases key in on the growth of third-party relationships with cloud service providers. The regulators encourage the use of:
- Core planning and assessment teams with requisite knowledge and skills across multiple disciplines, including relevant business lines, compliance, risk, technology, and legal.
- Industry utilities and consortiums to gain efficiencies in due diligence and ongoing monitoring (noting this is also a third-party relationship.)
Execute dynamic TPRM risk assessments, with clarity on direct and indirect risk assessment, measurements and contingencies.
Risk assessments are foundational to a risk-based TPRM program and should be conducted over the TPRM life cycle. Deficiencies may expose an organization to strategic, reputation, credit, operational, compliance, liquidity, and/or concentration risks.
Regulators expect risk assessment processes to:
- Engage all three lines of defense in an enterprise-wide approach and provide for board reporting on material risks, including mitigation and/or remediation efforts.
- Maintain and continuously update an inventory of risks based on direct experience, market developments, and/or strategic business changes along with an assessment of the effectiveness of existing controls.
- Subject third parties that support “critical activities,” are relied on to a “significant extent,” or entail greater risk and complexity to more comprehensive and rigorous oversight and monitoring.
- Consider transition, contingency, and recovery testing plans, including multi-cloud and key vendor duplicity strategies.
Ensure TPRM meets or exceed global and jurisdictional regulatory expectations.
The location of a third party (or fourth party) does not relieve the financial services company of its responsibility for compliance with all applicable laws and regulations, including ensuring that the third party also meets those obligations.
Regulators expect:
- Risk assessments will evaluate whether a third party has the expertise, processes, and controls to maintain its necessary licenses and enable the financial services company to remain compliant with domestic and international laws and regulations, as appropriate (key areas of jurisdictional differentiation include data privacy, information security, Bank Secrecy Act/anti-money laundering, sanctions, and fiduciary requirements).
- Contract provisions will clearly and thoroughly document the responsibilities of the company and the third party, including management of conflicts between the U.S. and foreign country requirements (e.g., data sharing, data access). (Note: regulators state a third-party relationship may exist despite a lack of contract or remuneration>)
- Consideration of potential or pending changes to the laws or regulations in the U.S. or the foreign country that could hinder fulfilment of the contract.
Use data sandboxes and parallel data proof of concept runs for changes to procurement and TPRM processes.
Testing the impact of changes in an environment isolated from a company’s critical infrastructure can provide opportunity to identify unexpected issues or challenges and make necessary adjustments without putting the company’s data at risk prior to full implementation. Such testing may highlight issues with data security, systems access, systems compatibility, talent needs (technology expertise, training, recruiting), governance, and reporting.
Noting the marked transition to cloud computing, regulators have placed a high priority on data and systems safeguards and focus on cybersecurity (authentication and access), data privacy, business continuity, and audit and controls. Sandboxes, proof of concept runs, and pilot programs allow a company to strengthen the cloud adoption and migration process.
Build a “zero trust” security environment with modern security tools and continuous monitoring for IT/Cyber controls.
Authentication risks are rising due to i) expanded remote access points, ii) the types of devices and third parties accessing information systems, iii) the use of application programming interfaces, and iv) increasing connectivity to third parties, such as cloud service providers. A “zero trust” security environment requires all users, both inside and outside of the company, to be authenticated, authorized, and continuously validated through real-time information from multiple sources before being granted or keeping access to applications and data. It is intended to limit a user’s access to only what is needed to complete a job.
Regulatory attention on zero-trust security systems is building and will be sustained.
- Federal agencies are now required to adopt and move toward implementing Zero Trust Architecture as part of their migration to cloud technology pursuant to Executive Order 14208 (May 2021) and consistent with migration steps as outlined by the National Institute of Standards and Technology (NIST). This may begin to set an expected standard for supervised entities.
- FFIEC guidance on systems authentication and access addresses many of the Zero Trust Architecture features, including multi-factor authentication, data encryption, identity protection, and endpoint security.
Ten Key Regulatory Challenges of 2022
The year 2022 brings high levels of risk and regulatory supervision and enforcement. Regulatory “perimeters” continue to expand, and regulatory expectations are rapidly increasing. All financial services companies should expect high levels of supervision and enforcement activity across ten key challenge areas. Read the full report to learn more.
Dive into our thinking:
Ten Key Regulatory Challenges of 2022
Download PDFExplore more
Meet our team



Get the latest from KPMG Regulatory Insights
KPMG Regulatory Insights is the thought leader hub for timely insight on risk and regulatory developments.
